Hello Readers, Whats Up? Hope You all should be fine enough to read this tutorial. As in
previous Article I said that i'll demonstrate that how to attack debuggable android applications. So This tutorial is about Finding and Attacking Debuggable Android Applications.
Before i start the procedure Let's collect the requirements.
and as in previous tutorial i told that
Android Tamer Have all these tools so no need to be worry just start up your android tamer and if you don't have , get it now.
Checking For Vulnerable Apps
First of all we need to learn that how to check if an app is vulnerable or no. to check this we need to find either the app is debuggable or no. and how to do it? Here comes the Role of UrduSecurity.
Just Download the vulnerable apk file from above given link and provide following command in your android tamer's terminal .
after You have done it, You have to Check
AndroidManifest.xml File in order to see either the app is debuggable or no. Provide the Following Command to do that.
- nano Vulnerable/AndroidManifest.xml
and if you see this Line there,
android:debuggable="true" , viola This app is vulnerable and you can pentest it.
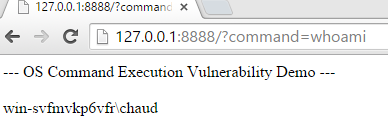
Exploiting the Vulnerable Application
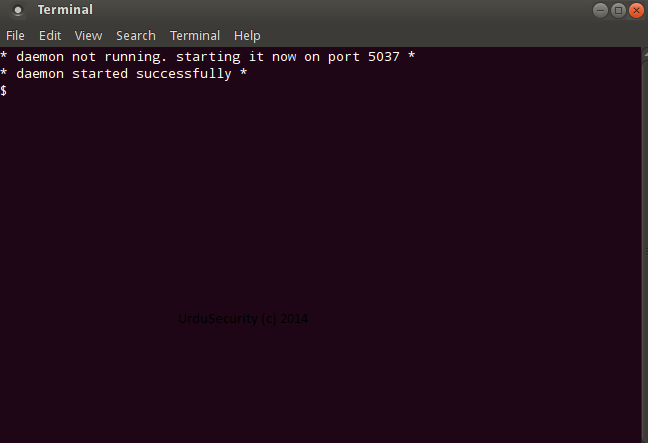
Now that You've got a vulnerable android app, Let's exploit it. start up your android emulator and launch the application. your goal is to change the text Try Again into Hacked By [UrduSecurity]. but first we have to check dalvik vm ports listening on emulator. give following command.
okay now we have to find on which port our
Vulnerable.apk is listening which you can find again by running the app and enumeratng the ports. Let's assume the app is litening on
1180 port so let's forward to this port and attach our terminal to the app using jdb debugger.
Now Let's Check the
classes and methods of
Vulnerable.apk and as our main class is
com.example.debug.MainActivity$1 so we'll be checking the
Methods of that class also. see below.
Now We have to set a break point at
onClick(android.view.View) method so that we can step through it and exploit the vulnerability by debugging the app.
- stop in com.example.debug.MainActivity$1.onClick(android.view.View)
and then check the position where we are by entering
locals in terminal. Finally we have to move
next by using the keyword
next. see below.
Please click on the app manually to re run the app as jdb don't provide this functionality here.
as in above figure , You have to step through all the steps untill you get the desired string, as we remember we have to replace
Try Again with
Hacked By UrduSecurity, so we found that string here. Now its time to step in the
secret = "Try Again" String.
and finally its time to give command
run , and you'll see that the app will automatically pop up our changed message that is:
Hacked By [UrduSecurity].
Yahooooooo, we just hacked the app. We can do a lot of other intresting stuff like getting a remote shell on victim and so on which we'll show you in later tutorials. Hope You've enjoyed this tutorial.
References
- infosecinstitute.com
- androidtamer.com
- oracle.com
- askubuntu.com