Hello Fans, currently Busy with a lot of things and i got exams too so i'll be lazy in updating the blog, well let's start Android Hacking as its the hottest topic to be discussed these days. This tutorial is a simple walk through of Android, adb shell & other Android Pentesting tools an sources.
Let's start it , hope you'll enjoy these Articles.
Basically all the Android devices are based on Linux Platform so A HAcker Must be aware of Linux environment in order to Play with android pentesting. There is a famous Virtual Lab Named as "Android Tamer" you can directly Download it From the Below Site.
http://androidtamer.com
i strongly suggest this Lab because it contains almost many of the tools used for android pentesting and as Hacking also means to be in touch with open source so it contains all open source tools about android aswell and for other pentesting stuff too.
after you've got your android tamer Lab Live & working. Now its time to Start Pentesting.
Rooted android device will be always a core requirement for these tutorials.
Here Starts our first tutorial about playing with basic things in android with adb shell and getting information.
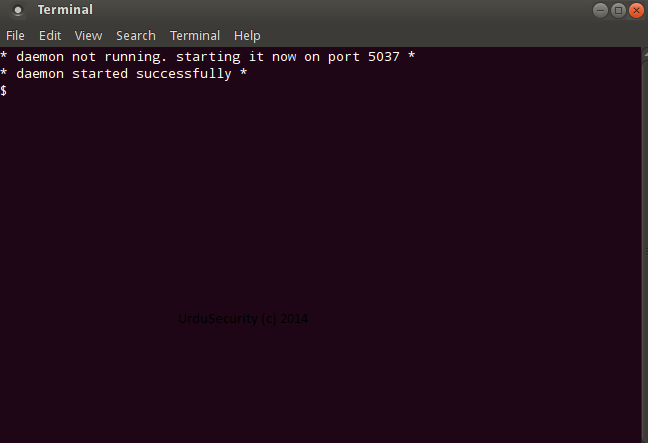
Enable USB Debugging Mode and Connect your android device with your android tamer Lab. Then do the same as shown in below screenshot.
if you've done it without any error , you should get a screen like this, that indicates that you got an adb shell on your android device.
Now that You are Connected with Your android device and Have a shell, Let's try to see the avaiable files there using "ls -l" command.
okay but till now we have only shell permissions, in order to gain root permissions we'll use 'su' command. see below.
Now we'll look at some files out there like gesture.key for Pattern Lock , as our pattern code is saved as salt sha-1 hashed form in gesture.key so let's look there.
and so on, Try to inspect it more via adb shell as we do in linux. and you'll get that where the data is stored basically and how the all stuff going ahead and working. in Next tutorial i'll Post How to debug and Find Vulnerable android applications.
Till Now if you have any problem , Let me know if i can solve. Thanks
Android Hacking: Getting Started with Android Pentesting
Views:














Completely agree. This blog provide valuable information on pentest and clearly show its importance. Thanks for sharing
ReplyDeleteHi All!
ReplyDeleteI'm selling fresh & genuine SSN Leads, with good connectivity. All data is tested & verified.
Headers in Leads:
First Name | Last Name | SSN | Dob | Address | State | City | Zip | Phone Number | Account Number | Bank NAME | DL Number | House Owner
*You can ask for sample before any deal
*Each SSN lead will be cost $1
*Premium Lead will be cost $5
*If anyone wants in bulk I will negotiate
*Sampling is just for serious buyers
Hope for the long term deal
For detailed information please contact me on:
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040