Introduction
Node.JS is a Cross Platform and
Runtime Environment Where one can execute javascript code, outside the Web
Browser. Node.JS is Very helpful but it has a couple of Killing features which
make it very dangerous and hazardous for a web application. In this tutorial we
are going to discuss one of them, Command Execution in Node.JS, You Folks must
know what is Command Execution but just to be sure I’d like to tell you,
Command Execution Vulnerabilities Allow an Attacker to run arbitrary Commands
on a System through the Vulnerable Environment. I guess its enough for
introcution.
Vulnerable
Code
Here is vulnerable code which demonstrates
the vulnerability in node js.
I’ll simply give the overview
about where exactly its getting hectic. We are using exec function from child_process
library, and executing parsedUrl.query.command,
that is not getting filtered. Hence an attacker can execute any arbitrary
commdn in order to hack into system. Let’s Save it and run it. Here is my
script running.
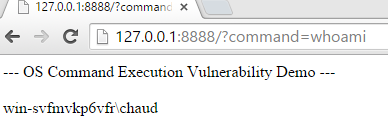
Code is working without any
error, let’s try to visit the url 127.0.0.1:8888
in browser as it is listening on port 8888.
Whoa, we got it working. Now its
time to do some evil stuff. Let’s try to execute systeminfo, PING & Some other commands , that displays
information about a computer.
#fig1
#fig2
#fig3
Okay fine, as it is clear from
the above POC that its working
exactly fine. In this context a developer must be careful while working with
Node.JS files as its kinda more hectic and Evil than other languages.
About the
Author
Muhammad
Adeel is a Security researcher & Founder at Whitehat Conference
Pakistan, he Blogs at http://urdusecurity.blogspot.com
Node JS & Command Execution
Views:














It’s a very informative and helpful article, thank you for sharing!
ReplyDeletemelbourne seo services
Web Security >>>>> Download Now
Delete>>>>> Download Full
Web Security >>>>> Download LINK
>>>>> Download Now
Web Security >>>>> Download Full
>>>>> Download LINK Ax
CLASSIC CYBER HACKS
ReplyDeleteHow well are you prepared for a Cyber incident or Breach?, Is your Data safe?
Strengthen your Cybersecurity stance by contacting CLASSIC CYBER NOTCH @ GMAIL DOT COM for a Perfect, Unique, Classic and Professional Job in Securing your Network against all sort of breaches and from scammers as well.
For we are Specially equipped with the Best hands to getting your Cyber Hack needs met as your jobs will be handled with utmost professionalism.
We do All type of cyber Jobs such as:
☑ TRACKING of GPS location, cars, Computers, Phones (Apple, windows and Android), e.t.c.
We also Track
E-MAIL account,(G-mail, Yahoo mail, AOL, Proton mail, etc.)
SOCIAL MEDIA account, (Facebook, Twitter, Skype, Whatsapp, e.t.c.)
☑ RECOVERY of Passwords for E-mail address, Phones, Computers, Social media Accounts, Documents e.t.c
☑ INSTALLATION of Spy ware so as to spy into someone else's computer, phone or E-mail address and also Installation of Spy ware software on your individual O.S so as to detect intrusion of any type.
We also Create and Install VIRUS into any desired computer gadget.
☑ CRACKING Websites, any desired gadget it computers or phones, CCTV Survelance camera, Data base (of both Private and Govt organization, such as Schools, Hospitals, Court houses, The FBI, NSA) e.t.c....
NOTE:
Other Jobs we do are:
☑ We provide Private Investigator service
☑ Clearing Criminal records of diverse type
☑ Binary Options fraud Recovery
☑ Bitcoin Mining
☑ Issuing of Blank ATM cards
☑ And many more... etc.
We assure you that your Job will be attended to with care and efficiency as it will be handled by the Best professional hands in Cyber literacy.
We also have a forum where you can get yourself equipped with Advanced hacking Knowledge..
CLASSIC CYBER HACKS gives you the Best service in the Hacking world as our Success rate is Top Notch
Be sure to 📱 💻 us via E-mail @
Classic cyber notch at gmail dot com
any time, any day to get the Best Professional hands involved in putting a smile on your face.
We're Classic Hacks
Signed,
Collins .A.
Web Security >>>>> Download Now
ReplyDelete>>>>> Download Full
Web Security >>>>> Download LINK
>>>>> Download Now
Web Security >>>>> Download Full
>>>>> Download LINK
TOOLS&FULLZ SHOP
ReplyDelete_______________
hi EveryonE!
Are you been stuck for looking valid products or been scammed by scammers
Here the Valid store available for all kind of tools,tutorials & Fullz with quality
Learn hacking and spamming and do it on your own way & enjoy..........
_______________
1)FRESHLY SPAMMED USA FULLZ
2)HACKING & SPAMMING TOOLS
3)TUTORIALS
_______________
*Contact*
*ICQ :748957107
*Telegram : @James307
*Skype : Jamesvince$
_______________
USA SSN FULLZ WITH ALL PERSONAL DATA+DL NUMBER
-FULLZ FOR PUA & SBA
-FULLZ FOR TAX REFUND
*fullz/lead with DL num
*SSN+DOB
*Premium info
*EIN PIN LEADS
(TAX RETURN)
*ELECTRONIC FILING LEADS
ID's Photos For any state (back & front)
________________
+US cc Fullz
+(Dead Fullz)
+(Email leads with Password)
+(Dumps track 1 & 2 with pin and without pin)
+HACKING & CARDING TUTORIALS
+SMTP LINUX
+SAFE SOCK
+CPANEL
+RDPs
+Spamming Tutorial
+SERVER I.Ps
+EMAIL COMBO
+DUMPS TUTORIAL
+BTC FLASHER
+KEYLOGGER COMP&MOB
+EMAIL BOMBER
+SQLI INJECTOR
+ETHICAL HACKING TUTORIAL
+GMAIL HACKING TUTORIAL
+PENETRATION TESTING TUTORIAL
+PayPal Cracker
+BTC Cracker
+BLUE PRINTS BLOCKCHAIN
+EMAIL BLASTER
+SMS SENDER
+NORD VPN
+ONION LINKS AND TOR BROWSER (LATEST VERSION)
+DARK HORSE TROJAN
+NETFLIX CHECKER
+IP ROUTING
+KEYSTROKE LOGGER
+WESTERN UNION LOGINs
+ALI BABA IPs
+KEYLOGGER
+SHELL SCRIPTING
_______________
*Let's do a long term business with good profit
*Contact for more details & deal
*Contact*
*ICQ :748957107
*Telegram :@James307
*Skype : Jamesvince$
ReplyDeleteSSN | SIN| NIN | REAL DL F\B | EIN | PASSPORT | LTD | # TAXREFUND |
>SSN FULLZ USA REAL DOCS ID|DL FRONT BACK
>DL FULLZ MVR
>UK NIN DOB ADDRESS SORT CODE FULLZ
>UK NIN DOB DL ADDRESS MMN INFO PROS
>UK CANADA RUS FR IT GR DL|ID FRONT BACK WITH SELFIE
>PASSPORT PHOTOS WITH SELFIE
>BUSINESS EIN COMPANY FULLZ PROS
>YOUNG & OLD AGE FULLZ
>HIGH CREDIT SCORES PROS FULLZ
>SSN DOB DL FULLZ WITH ISSUE & EXPIRY DATES
>DEAD FULLZ UK USA CANADA
Telegram 💬 { @Zavi_24 }
Channel---{{ https://t.me/FullzDatabase24 }}
SIGNAL { @Leads_Providers.07
#USALEADS #UKFULLZ #CANADAFULLZ #FULLZPROS #SSNDOB #TAXRETURN26 #CRYPTOLEADS
#SINFULLZ #CCINFOS #Fullzwarehouse24
We have Tax Refund , W-2
Sell Info Fullz SSN DOB DL use it to do PUA and SBA
Sell Info FULLZ Applying For unemployment insurance benefit.
Sell Info for red Account Ebay and Amazon , Bank
Sell Info SSN + DOB + DOC + DL scan front & back is Real 100%